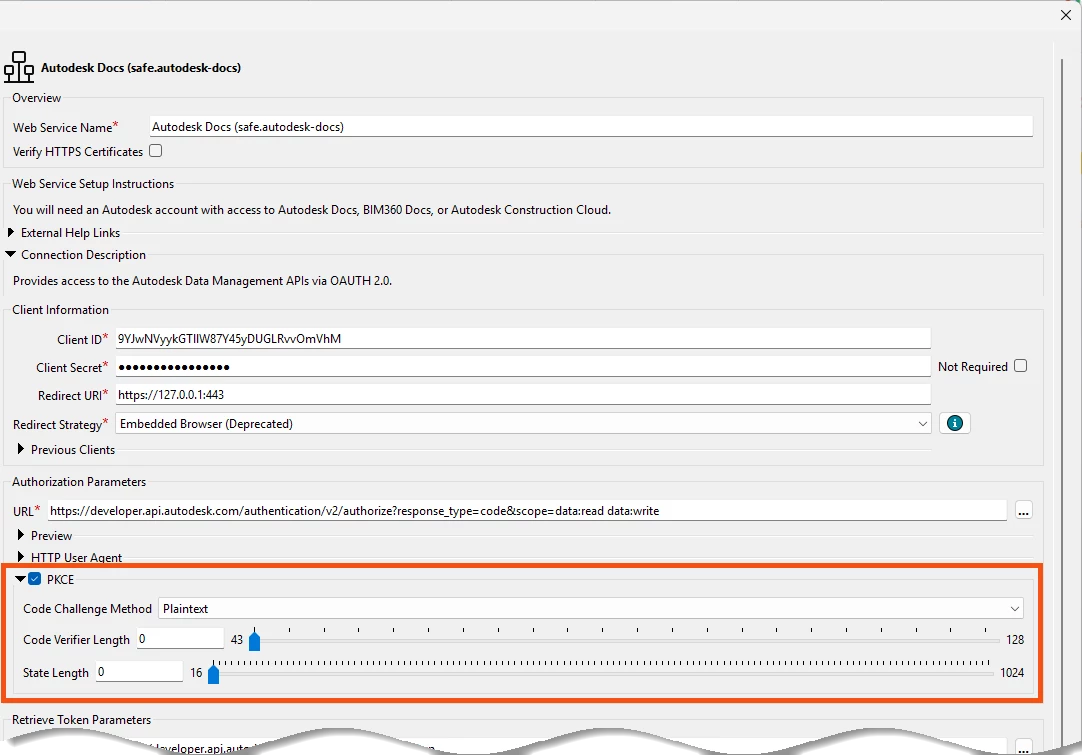
It seems I have no place to force FME to include the code_verifier parameter in the request body to obtain a token (see requirements below). Any ideas of how to work around this in FME? The postman equivalent is selecting the grant type as "Authorization Code (with PKCE)". I can use the same challenge and verifier more than once, just need to include it in the body rather than a querystring.
Per the platform's API docs:
Parameters sent in Request Body, Form-URL Encoded. (cannot use JSON or querystring)
code=<code received in callback url>
client_id=<Application OAuth Client ID>
client_secret=<Application OAuth Client Secret>
grant_type=authorization_code
redirect_uri=<User redirect URL (from step 4)>
code_verifier=<User Generated Code Verifier>